-
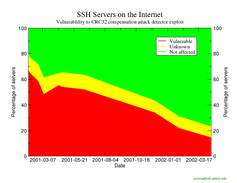
Vulnerability to CRC32 compensation attack detector exploit
In February 2001, Razor Bindview released their "Remote vulnerability in SSH daemon crc32 compensation attack detector" advisory, which outlined a gaping hole in deployed SSH servers that can lead to a remote attacker gaining privileged access.In November 2001, Dave Dittrich published a detailed analysis of the "CRC32 compensation attack detector exploit." This exploit is currently widely in use. CERT released CERT Incident Note IN-2001-12.
At the Center for Information Technology Integration, Niels Provos and Peter Honeyman have been scanning the University of Michigan to identify and update vulnerable SSH servers.
However, scans of the Internet show that system and security administrators must react and update their SSH servers:
-
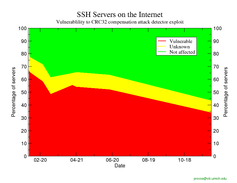
At this writing, over 30% of all SSH servers appear to have the CRC32 bug. To protect yourself, you need to update your SSH server software.
-
To test whether your network has vulnerable SSH
servers, you might use the ScanSSH
tool.
References:
-
- ScanSSH - Scanning the Internet for SSH Servers
- Niels Provos and Peter Honeyman, 16th USENIX Systems Administration Conference (LISA). San Diego, CA, December 2001.
-